Recently, our team found a vulnerability causing the arbitrary user role save in the latest version of the project.
The vulnerability logic is present in the file: https://gitee.com/tiankong0310/my-shop/blob/master/my-shop-shiro/src/main/java/com/fengdu/service/impl/SysUserServiceImpl.java#51.
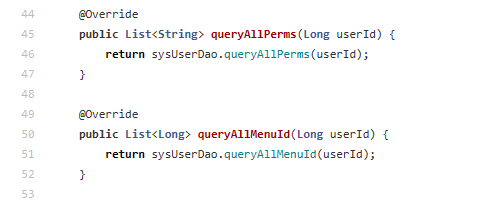
The developer failed to check the privilege of the accessor when updating status via com.fengdu.dao.SysUserDao.queryAllMenuId(), while the request of path /save is also unauthorized (i.e., https://gitee.com/tiankong0310/my-shop/blob/master/my-shop-shiro/src/main/java/com/fengdu/controller/SysRoleController.java#102), which means an attacker can achieve arbitrary user role save.
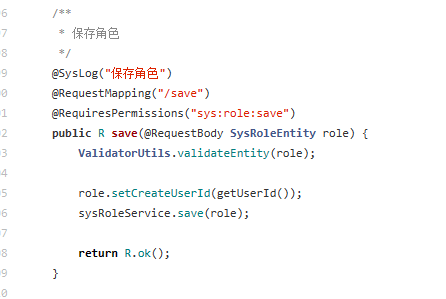
To address this vulnerability, we strongly advise that developers implement access control policies that limit API access to admin users or the owner.